La tua azienda è già onlife?
Seguici nei percorsi della
DIGITALTRANSFORMATION
Customer Engagement
Coinvolgi i visitatori dei tuoi spazi fisici e digitali (phygital) grazie a un'esperienza omnicanale che crea continuità tra le piattaforme di e-commerce e comunicazione online e gli allestimenti multimediali resi intelligenti e interattivi grazie a tecnologie domotiche, IoT e smart digital signage.
Employee empowerment
Aumenta la produttività e il coinvolgimento dei tuoi dipendenti grazie ad uno spazio di lavoro moderno e in cloud che consente di svolgere attività in ogni luogo in totale sicurezza e abilitare la collaboration.
Operation optimization
Semplifica i processi e aumenta l'efficienza per ridurre i costi e valorizzare le risorse grazie alle opportunità messe a disposizione da dati, cloud, IoT e Intelligenza Artificiale.
Business transformation
Aumenta il vantaggio competitivo della tua azienda ed entra rapidamente in nuovi mercati sfruttando le opportunità di business emergenti grazie ad una strategia data driven.
CASE STUDY
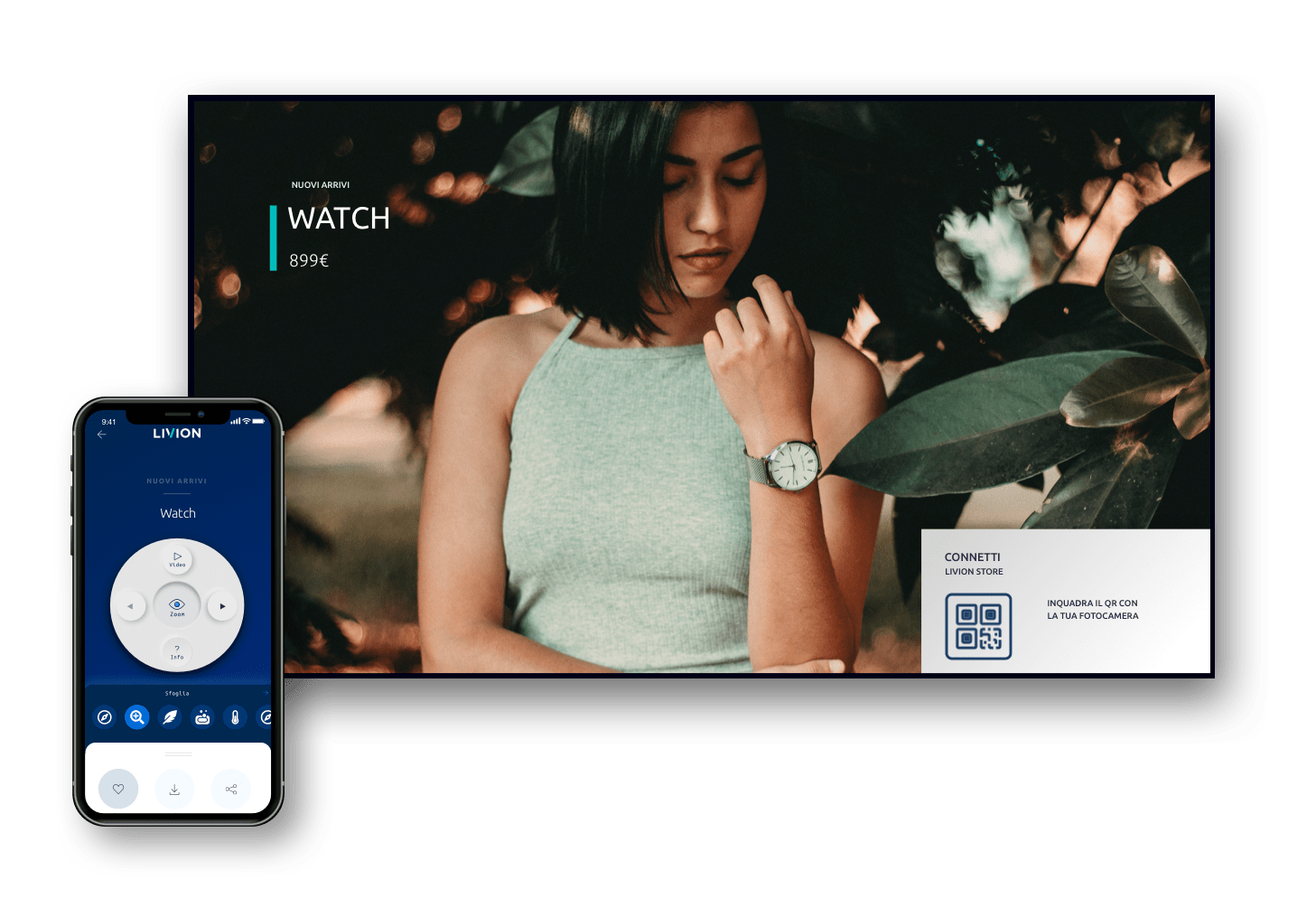
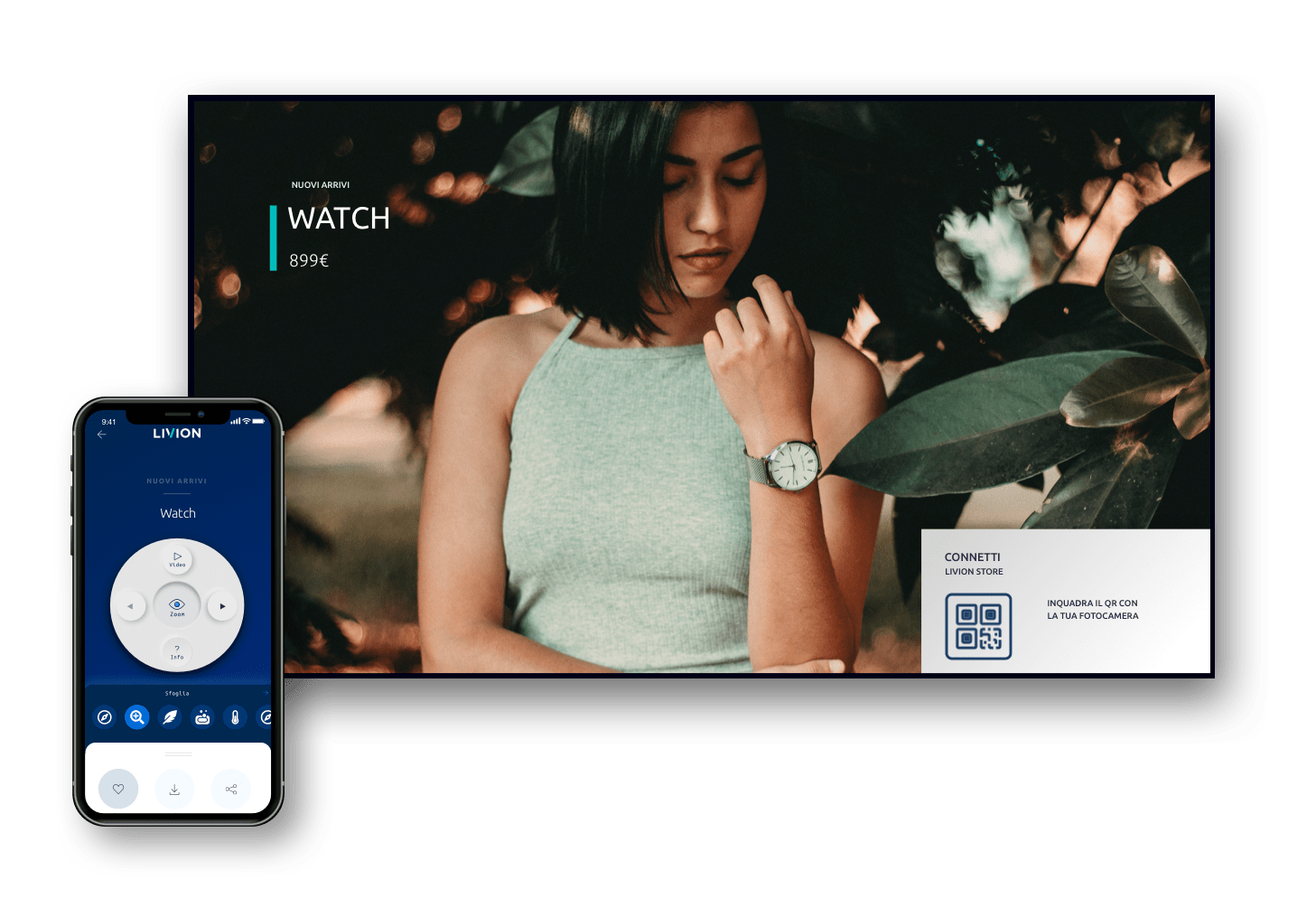
Smart Digital Signage
LIVION
Trasforma i tuoi spazi in ambienti intelligenti per gestire in sicurezza i flussi di persone e costruire percorsi multimediali personalizzati che coinvolgono i visitatori e li fidelizzano al brand.